CISA Exam Question 46
.Which of the following is an effective method for controlling downloading of files via FTP? Choose the BEST answer.
Correct Answer: B
Application-layer gateways, or proxy firewalls, are an effective method for controlling downloading of files via FTP. Because FTP is an OSI application-layer protocol, the most effective firewall needs to be capable of inspecting through the application layer.
CISA Exam Question 47
To reduce the possibility of losing data during processing, the FIRST point at which control totals should be implemented is:
Correct Answer: A
Explanation/Reference:
Explanation:
During data preparation is the best answer, because it establishes control at the earliest point.
Explanation:
During data preparation is the best answer, because it establishes control at the earliest point.
CISA Exam Question 48
An organization that has outsourced its incident management capabilities just discovered a significant
privacy breach by an unknown attacker. Which of the following is the MOST important action of the security
manager?
privacy breach by an unknown attacker. Which of the following is the MOST important action of the security
manager?
Correct Answer: C
Section: Information System Operations, Maintenance and Support
CISA Exam Question 49
Which of the following layer of an OSI model ensures that messages are delivered error-free, in sequence,
and with no losses or duplications?
and with no losses or duplications?
Correct Answer: D
Section: Information System Operations, Maintenance and Support
Explanation
Explanation/Reference:
The transport layer ensures that messages are delivered error-free, in sequence, and with no losses or
duplications. It relieves the higher layer protocols from any concern with the transfer of data between them
and their peers.
The size and complexity of a transport protocol depends on the type of service it can get from the network
layer. For a reliable network layer with virtual circuit capability, a minimal transport layer is required. If the
network layer is unreliable and/or only supports datagram's, the transport protocol should include extensive
error detection and recovery.
The transport layer provides:
Message segmentation: accepts a message from the (session) layer above it, splits the message into
smaller units (if not already small enough), and passes the smaller units down to the network layer. The
transport layer at the destination station reassembles the message.
Message acknowledgment: provides reliable end-to-end message delivery with acknowledgments.
Message traffic control: tells the transmitting station to "back-off" when no message buffers are available.
Session multiplexing: multiplexes several message streams, or sessions onto one logical link and keeps
track of which messages belong to which sessions (see session layer).
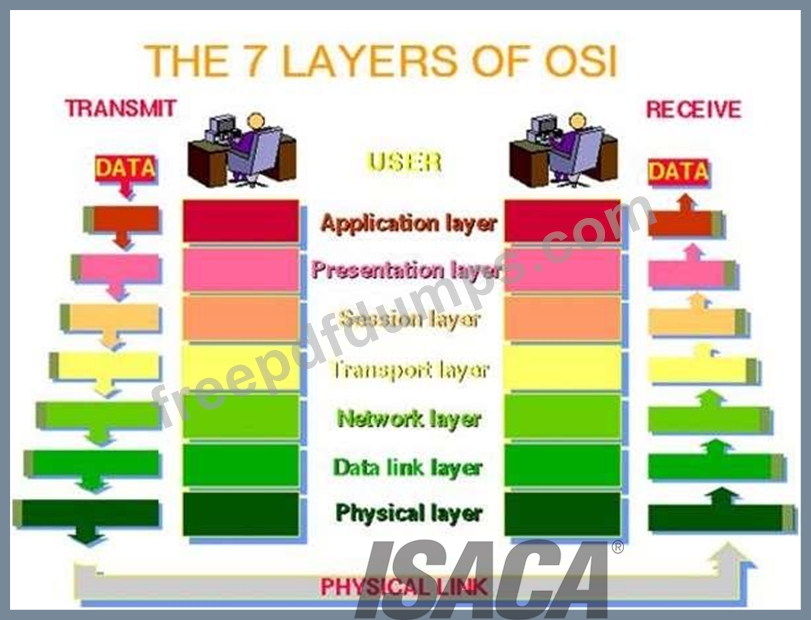
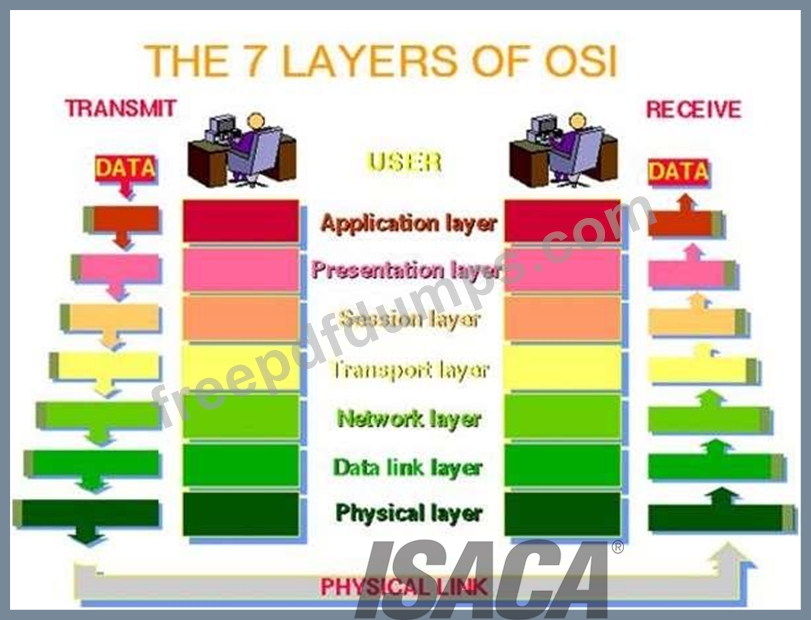
For your exam you should know below information about OSI model:
The Open Systems Interconnection model (OSI) is a conceptual model that characterizes and standardizes
the internal functions of a communication system by partitioning it into abstraction layers. The model is a
product of the Open Systems Interconnection project at the International Organization for Standardization
(ISO), maintained by the identification ISO/IEC 7498-1.
The model groups communication functions into seven logical layers. A layer serves the layer above it and
is served by the layer below it. For example, a layer that provides error-free communications across a
network provides the path needed by applications above it, while it calls the next lower layer to send and
receive packets that make up the contents of that path. Two instances at one layer are connected by a
horizontal.
OSI Model
PHYSICAL LAYER
The physical layer, the lowest layer of the OSI model, is concerned with the transmission and reception of
the unstructured raw bit stream over a physical medium. It describes the electrical/optical, mechanical, and
functional interfaces to the physical medium, and carries the signals for all of the higher layers. It provides:
Data encoding: modifies the simple digital signal pattern (1s and 0s) used by the PC to better
accommodate the characteristics of the physical medium, and to aid in bit and frame synchronization. It
determines:
What signal state represents a binary 1
How the receiving station knows when a "bit-time" starts
How the receiving station delimits a frame
DATA LINK LAYER
The data link layer provides error-free transfer of data frames from one node to another over the physical
layer, allowing layers above it to assume virtually error-free transmission over the link. To do this, the data
link layer provides:
Link establishment and termination: establishes and terminates the logical link between two nodes.
Frame traffic control: tells the transmitting node to "back-off" when no frame buffers are available.
Frame sequencing: transmits/receives frames sequentially.
Frame acknowledgment: provides/expects frame acknowledgments. Detects and recovers from errors that
occur in the physical layer by retransmitting non-acknowledged frames and handling duplicate frame
receipt.
Frame delimiting: creates and recognizes frame boundaries.
Frame error checking: checks received frames for integrity.
Media access management: determines when the node "has the right" to use the physical medium.
NETWORK LAYER
The network layer controls the operation of the subnet, deciding which physical path the data should take
based on network conditions, priority of service, and other factors. It provides:
Routing: routes frames among networks.
Subnet traffic control: routers (network layer intermediate systems) can instruct a sending station to
"throttle back" its frame transmission when the router's buffer fills up.
Frame fragmentation: if it determines that a downstream router's maximum transmission unit (MTU) size is
less than the frame size, a router can fragment a frame for transmission and re-assembly at the destination
station.
Logical-physical address mapping: translates logical addresses, or names, into physical addresses.
Subnet usage accounting: has accounting functions to keep track of frames forwarded by subnet
intermediate systems, to produce billing information.
Communications Subnet
The network layer software must build headers so that the network layer software residing in the subnet
intermediate systems can recognize them and use them to route data to the destination address.
This layer relieves the upper layers of the need to know anything about the data transmission and
intermediate switching technologies used to connect systems. It establishes, maintains and terminates
connections across the intervening communications facility (one or several intermediate systems in the
communication subnet).
In the network layer and the layers below, peer protocols exist between a node and its immediate neighbor,
but the neighbor may be a node through which data is routed, not the destination station. The source and
destination stations may be separated by many intermediate systems.
TRANSPORT LAYER
The transport layer ensures that messages are delivered error-free, in sequence, and with no losses or
duplications. It relieves the higher layer protocols from any concern with the transfer of data between them
and their peers.
The size and complexity of a transport protocol depends on the type of service it can get from the network
layer. For a reliable network layer with virtual circuit capability, a minimal transport layer is required. If the
network layer is unreliable and/or only supports datagram's, the transport protocol should include extensive
error detection and recovery.
The transport layer provides:
Message segmentation: accepts a message from the (session) layer above it, splits the message into
smaller units (if not already small enough), and passes the smaller units down to the network layer. The
transport layer at the destination station reassembles the message.
Message acknowledgment: provides reliable end-to-end message delivery with acknowledgments.
Message traffic control: tells the transmitting station to "back-off" when no message buffers are available.
Session multiplexing: multiplexes several message streams, or sessions onto one logical link and keeps
track of which messages belong to which sessions (see session layer).
Typically, the transport layer can accept relatively large messages, but there are strict message size limits
imposed by the network (or lower) layer. Consequently, the transport layer must break up the messages
into smaller units, or frames, pretending a header to each frame.
The transport layer header information must then include control information, such as message start and
message end flags, to enable the transport layer on the other end to recognize message boundaries. In
addition, if the lower layers do not maintain sequence, the transport header must contain sequence
information to enable the transport layer on the receiving end to get the pieces back together in the right
order before handing the received message up to the layer above.
End-to-end layers
Unlike the lower "subnet" layers whose protocol is between immediately adjacent nodes, the transport layer
and the layers above are true "source to destination" or end-to-end layers, and are not concerned with the
details of the underlying communications facility. Transport layer software (and software above it) on the
source station carries on a conversation with similar software on the destination station by using message
headers and control messages.
SESSION LAYER
The session layer allows session establishment between processes running on different stations. It
provides:
Session establishment, maintenance and termination: allows two application processes on different
machines to establish, use and terminate a connection, called a session.
Session support: performs the functions that allow these processes to communicate over the network,
performing security, name recognition, logging, and so on.
PRESENTATION LAYER
The presentation layer formats the data to be presented to the application layer. It can be viewed as the
translator for the network. This layer may translate data from a format used by the application layer into a
common format at the sending station, then translate the common format to a format known to the
application layer at the receiving station.
The presentation layer provides:
Character code translation: for example, ASCII to EBCDIC.
Data conversion: bit order, CR-CR/LF, integer-floating point, and so on.
Data compression: reduces the number of bits that need to be transmitted on the network.
Data encryption: encrypt data for security purposes. For example, password encryption.
APPLICATION LAYER
The application layer serves as the window for users and application processes to access network
services. This layer contains a variety of commonly needed functions:
Resource sharing and device redirection
Remote file access
Remote printer access
Inter-process communication
Network management
Directory services
Electronic messaging (such as mail)
Network virtual terminals
The following were incorrect answers:
Application Layer - The application layer serves as the window for users and application processes to
access network services.
Presentation layer - The presentation layer formats the data to be presented to the application layer. It can
be viewed as the translator for the network. This layer may translate data from a format used by the
application layer into a common format at the sending station, then translate the common format to a
format known to the application layer at the receiving station.
Session layer - The session layer allows session establishment between processes running on different
stations.
The following reference(s) were/was used to create this question:
CISA review manual 2014 Page number 260
Explanation
Explanation/Reference:
The transport layer ensures that messages are delivered error-free, in sequence, and with no losses or
duplications. It relieves the higher layer protocols from any concern with the transfer of data between them
and their peers.
The size and complexity of a transport protocol depends on the type of service it can get from the network
layer. For a reliable network layer with virtual circuit capability, a minimal transport layer is required. If the
network layer is unreliable and/or only supports datagram's, the transport protocol should include extensive
error detection and recovery.
The transport layer provides:
Message segmentation: accepts a message from the (session) layer above it, splits the message into
smaller units (if not already small enough), and passes the smaller units down to the network layer. The
transport layer at the destination station reassembles the message.
Message acknowledgment: provides reliable end-to-end message delivery with acknowledgments.
Message traffic control: tells the transmitting station to "back-off" when no message buffers are available.
Session multiplexing: multiplexes several message streams, or sessions onto one logical link and keeps
track of which messages belong to which sessions (see session layer).
For your exam you should know below information about OSI model:
The Open Systems Interconnection model (OSI) is a conceptual model that characterizes and standardizes
the internal functions of a communication system by partitioning it into abstraction layers. The model is a
product of the Open Systems Interconnection project at the International Organization for Standardization
(ISO), maintained by the identification ISO/IEC 7498-1.
The model groups communication functions into seven logical layers. A layer serves the layer above it and
is served by the layer below it. For example, a layer that provides error-free communications across a
network provides the path needed by applications above it, while it calls the next lower layer to send and
receive packets that make up the contents of that path. Two instances at one layer are connected by a
horizontal.
OSI Model
PHYSICAL LAYER
The physical layer, the lowest layer of the OSI model, is concerned with the transmission and reception of
the unstructured raw bit stream over a physical medium. It describes the electrical/optical, mechanical, and
functional interfaces to the physical medium, and carries the signals for all of the higher layers. It provides:
Data encoding: modifies the simple digital signal pattern (1s and 0s) used by the PC to better
accommodate the characteristics of the physical medium, and to aid in bit and frame synchronization. It
determines:
What signal state represents a binary 1
How the receiving station knows when a "bit-time" starts
How the receiving station delimits a frame
DATA LINK LAYER
The data link layer provides error-free transfer of data frames from one node to another over the physical
layer, allowing layers above it to assume virtually error-free transmission over the link. To do this, the data
link layer provides:
Link establishment and termination: establishes and terminates the logical link between two nodes.
Frame traffic control: tells the transmitting node to "back-off" when no frame buffers are available.
Frame sequencing: transmits/receives frames sequentially.
Frame acknowledgment: provides/expects frame acknowledgments. Detects and recovers from errors that
occur in the physical layer by retransmitting non-acknowledged frames and handling duplicate frame
receipt.
Frame delimiting: creates and recognizes frame boundaries.
Frame error checking: checks received frames for integrity.
Media access management: determines when the node "has the right" to use the physical medium.
NETWORK LAYER
The network layer controls the operation of the subnet, deciding which physical path the data should take
based on network conditions, priority of service, and other factors. It provides:
Routing: routes frames among networks.
Subnet traffic control: routers (network layer intermediate systems) can instruct a sending station to
"throttle back" its frame transmission when the router's buffer fills up.
Frame fragmentation: if it determines that a downstream router's maximum transmission unit (MTU) size is
less than the frame size, a router can fragment a frame for transmission and re-assembly at the destination
station.
Logical-physical address mapping: translates logical addresses, or names, into physical addresses.
Subnet usage accounting: has accounting functions to keep track of frames forwarded by subnet
intermediate systems, to produce billing information.
Communications Subnet
The network layer software must build headers so that the network layer software residing in the subnet
intermediate systems can recognize them and use them to route data to the destination address.
This layer relieves the upper layers of the need to know anything about the data transmission and
intermediate switching technologies used to connect systems. It establishes, maintains and terminates
connections across the intervening communications facility (one or several intermediate systems in the
communication subnet).
In the network layer and the layers below, peer protocols exist between a node and its immediate neighbor,
but the neighbor may be a node through which data is routed, not the destination station. The source and
destination stations may be separated by many intermediate systems.
TRANSPORT LAYER
The transport layer ensures that messages are delivered error-free, in sequence, and with no losses or
duplications. It relieves the higher layer protocols from any concern with the transfer of data between them
and their peers.
The size and complexity of a transport protocol depends on the type of service it can get from the network
layer. For a reliable network layer with virtual circuit capability, a minimal transport layer is required. If the
network layer is unreliable and/or only supports datagram's, the transport protocol should include extensive
error detection and recovery.
The transport layer provides:
Message segmentation: accepts a message from the (session) layer above it, splits the message into
smaller units (if not already small enough), and passes the smaller units down to the network layer. The
transport layer at the destination station reassembles the message.
Message acknowledgment: provides reliable end-to-end message delivery with acknowledgments.
Message traffic control: tells the transmitting station to "back-off" when no message buffers are available.
Session multiplexing: multiplexes several message streams, or sessions onto one logical link and keeps
track of which messages belong to which sessions (see session layer).
Typically, the transport layer can accept relatively large messages, but there are strict message size limits
imposed by the network (or lower) layer. Consequently, the transport layer must break up the messages
into smaller units, or frames, pretending a header to each frame.
The transport layer header information must then include control information, such as message start and
message end flags, to enable the transport layer on the other end to recognize message boundaries. In
addition, if the lower layers do not maintain sequence, the transport header must contain sequence
information to enable the transport layer on the receiving end to get the pieces back together in the right
order before handing the received message up to the layer above.
End-to-end layers
Unlike the lower "subnet" layers whose protocol is between immediately adjacent nodes, the transport layer
and the layers above are true "source to destination" or end-to-end layers, and are not concerned with the
details of the underlying communications facility. Transport layer software (and software above it) on the
source station carries on a conversation with similar software on the destination station by using message
headers and control messages.
SESSION LAYER
The session layer allows session establishment between processes running on different stations. It
provides:
Session establishment, maintenance and termination: allows two application processes on different
machines to establish, use and terminate a connection, called a session.
Session support: performs the functions that allow these processes to communicate over the network,
performing security, name recognition, logging, and so on.
PRESENTATION LAYER
The presentation layer formats the data to be presented to the application layer. It can be viewed as the
translator for the network. This layer may translate data from a format used by the application layer into a
common format at the sending station, then translate the common format to a format known to the
application layer at the receiving station.
The presentation layer provides:
Character code translation: for example, ASCII to EBCDIC.
Data conversion: bit order, CR-CR/LF, integer-floating point, and so on.
Data compression: reduces the number of bits that need to be transmitted on the network.
Data encryption: encrypt data for security purposes. For example, password encryption.
APPLICATION LAYER
The application layer serves as the window for users and application processes to access network
services. This layer contains a variety of commonly needed functions:
Resource sharing and device redirection
Remote file access
Remote printer access
Inter-process communication
Network management
Directory services
Electronic messaging (such as mail)
Network virtual terminals
The following were incorrect answers:
Application Layer - The application layer serves as the window for users and application processes to
access network services.
Presentation layer - The presentation layer formats the data to be presented to the application layer. It can
be viewed as the translator for the network. This layer may translate data from a format used by the
application layer into a common format at the sending station, then translate the common format to a
format known to the application layer at the receiving station.
Session layer - The session layer allows session establishment between processes running on different
stations.
The following reference(s) were/was used to create this question:
CISA review manual 2014 Page number 260
CISA Exam Question 50
What is an edit check to determine whether a field contains valid data?
Correct Answer: A
Explanation/Reference:
A completeness check is an edit check to determine whether a field contains valid data.
A completeness check is an edit check to determine whether a field contains valid data.
- Other Version
- 735ISACA.CISA.v2025-12-09.q630
- 415ISACA.CISA.v2025-12-02.q704
- 10539ISACA.CISA.v2025-06-20.q647
- 3532ISACA.CISA.v2025-06-11.q606
- 3411ISACA.CISA.v2023-03-04.q272
- 2655ISACA.CISA.v2022-10-31.q203
- 2595ISACA.CISA.v2022-03-29.q126
- 123ISACA.Examprepaway.CISA.v2022-02-10.by.barret.126q.pdf
- 36ISACA.Actualvce.CISA.v2021-08-31.by.ralap.101q.pdf
- Latest Upload
- 119SAP.C_BCBAI_2509.v2026-01-15.q13
- 198DAMA.DMF-1220.v2026-01-15.q271
- 138SAP.C_SIGDA_2403.v2026-01-15.q66
- 187ISACA.CRISC.v2026-01-15.q649
- 128PaloAltoNetworks.NetSec-Pro.v2026-01-15.q26
- 170Splunk.SPLK-1002.v2026-01-14.q121
- 170EMC.NCP-AII.v2026-01-14.q144
- 164Microsoft.AZ-800.v2026-01-13.q144
- 176Microsoft.MS-102.v2026-01-13.q258
- 121HP.HPE2-E84.v2026-01-13.q17
[×]
Download PDF File
Enter your email address to download ISACA.CISA.v2021-11-29.q567 Practice Test

