CISA Exam Question 86
During an IS audit, auditor has observed that authentication and authorization steps are split into two functions and there is a possibility to force the authorization step to be completed before the authentication step. Which of the following technique an attacker could user to force authorization step before authentication?
Correct Answer: D
Explanation/Reference:
A race condition is when processes carry out their tasks on a shared resource in an incorrect order. A race condition is possible when two or more processes use a shared resource, as in data within a variable. It is important that the processes carry out their functionality in the correct sequence. If process 2 carried out its task on the data before process 1, the result will be much different than if process1 carried out its tasks on the data before process 2.
In software, when the authentication and authorization steps are split into two functions, there is a possibility an attacker could use a race condition to force the authorization step to be completed before the authentication step. This would be a flaw in the software that the attacker has figured out how to exploit. A race condition occurs when two or more processes use the same resource and the sequences of steps within the software can be carried out in an improper order, something that can drastically affect the output.
So, an attacker can force the authorization step to take place before the authentication step and gain unauthorized access to a resource.
The following answers are incorrect:
Eavesdropping - is the act of secretly listening to the private conversation of others without their consent, as defined by Black's Law Dictionary. This is commonly thought to be unethical and there is an old adage that "eavesdroppers seldom hear anything good of themselves...eavesdroppers always try to listen to matters that concern them." Traffic analysis - is the process of intercepting and examining messages in order to deduce information from patterns in communication. It can be performed even when the messages are encrypted and cannot be decrypted. In general, the greater the number of messages observed, or even intercepted and stored, the more can be inferred from the traffic. Traffic analysis can be performed in the context of military intelligence, counter-intelligence, or pattern-of-life analysis, and is a concern in computer security.
Masquerading - A masquerade attack is an attack that uses a fake identity, such as a network identity, to gain unauthorized access to personal computer information through legitimate access identification. If an authorization process is not fully protected, it can become extremely vulnerable to a masquerade attack.
Masquerade attacks can be perpetrated using stolen passwords and logons, by locating gaps in programs, or by finding a way around the authentication process. The attack can be triggered either by someone within the organization or by an outsider if the organization is connected to a public network. The amount of access masquerade attackers get depends on the level of authorization they've managed to attain. As such, masquerade attackers can have a full smorgasbord of cyber crime opportunities if they've gained the highest access authority to a business organization. Personal attacks, although less common, can also be harmful.
Following reference(s) were/was used to create this question:
CISA review manual 2014 Page number 324
Official ISC2 guide to CISSP CBK 3rd Edition Page number 66
CISSP All-In-One Exam guide 6th Edition Page Number 161
A race condition is when processes carry out their tasks on a shared resource in an incorrect order. A race condition is possible when two or more processes use a shared resource, as in data within a variable. It is important that the processes carry out their functionality in the correct sequence. If process 2 carried out its task on the data before process 1, the result will be much different than if process1 carried out its tasks on the data before process 2.
In software, when the authentication and authorization steps are split into two functions, there is a possibility an attacker could use a race condition to force the authorization step to be completed before the authentication step. This would be a flaw in the software that the attacker has figured out how to exploit. A race condition occurs when two or more processes use the same resource and the sequences of steps within the software can be carried out in an improper order, something that can drastically affect the output.
So, an attacker can force the authorization step to take place before the authentication step and gain unauthorized access to a resource.
The following answers are incorrect:
Eavesdropping - is the act of secretly listening to the private conversation of others without their consent, as defined by Black's Law Dictionary. This is commonly thought to be unethical and there is an old adage that "eavesdroppers seldom hear anything good of themselves...eavesdroppers always try to listen to matters that concern them." Traffic analysis - is the process of intercepting and examining messages in order to deduce information from patterns in communication. It can be performed even when the messages are encrypted and cannot be decrypted. In general, the greater the number of messages observed, or even intercepted and stored, the more can be inferred from the traffic. Traffic analysis can be performed in the context of military intelligence, counter-intelligence, or pattern-of-life analysis, and is a concern in computer security.
Masquerading - A masquerade attack is an attack that uses a fake identity, such as a network identity, to gain unauthorized access to personal computer information through legitimate access identification. If an authorization process is not fully protected, it can become extremely vulnerable to a masquerade attack.
Masquerade attacks can be perpetrated using stolen passwords and logons, by locating gaps in programs, or by finding a way around the authentication process. The attack can be triggered either by someone within the organization or by an outsider if the organization is connected to a public network. The amount of access masquerade attackers get depends on the level of authorization they've managed to attain. As such, masquerade attackers can have a full smorgasbord of cyber crime opportunities if they've gained the highest access authority to a business organization. Personal attacks, although less common, can also be harmful.
Following reference(s) were/was used to create this question:
CISA review manual 2014 Page number 324
Official ISC2 guide to CISSP CBK 3rd Edition Page number 66
CISSP All-In-One Exam guide 6th Edition Page Number 161
CISA Exam Question 87
Which of the following attack occurs when a malicious action is performed by invoking the operating system to execute a particular system call?
Correct Answer: D
Explanation/Reference:
An Interrupt attack occurs when a malicious action is performed by invoking the operating system to execute a particular system call.
Example: A boot sector virus typically issue an interrupt to execute a write to the boot sector.
The following answers are incorrect:
Eavesdropping - is the act of secretly listening to the private conversation of others without their consent, as defined by Black's Law Dictionary. This is commonly thought to be unethical and there is an old adage that "eavesdroppers seldom hear anything good of themselves...eavesdroppers always try to listen to matters that concern them."
Traffic analysis - is the process of intercepting and examining messages in order to deduce information from patterns in communication. It can be performed even when the messages are encrypted and cannot be decrypted. In general, the greater the number of messages observed, or even intercepted and stored, the more can be inferred from the traffic. Traffic analysis can be performed in the context of military intelligence, counter-intelligence, or pattern-of-life analysis, and is a concern in computer security.
Masquerading - A masquerade attack is an attack that uses a fake identity, such as a network identity, to gain unauthorized access to personal computer information through legitimate access identification. If an authorization process is not fully protected, it can become extremely vulnerable to a masquerade attack.
Masquerade attacks can be perpetrated using stolen passwords and logons, by locating gaps in programs, or by finding a way around the authentication process. The attack can be triggered either by someone within the organization or by an outsider if the organization is connected to a public network. The amount of access masquerade attackers get depends on the level of authorization they've managed to attain. As such, masquerade attackers can have a full smorgasbord of cyber crime opportunities if they've gained the highest access authority to a business organization. Personal attacks, although less common, can also be harmful.
Following reference(s) were/was used to create this question:
CISA review manual 2014 Page number 322
An Interrupt attack occurs when a malicious action is performed by invoking the operating system to execute a particular system call.
Example: A boot sector virus typically issue an interrupt to execute a write to the boot sector.
The following answers are incorrect:
Eavesdropping - is the act of secretly listening to the private conversation of others without their consent, as defined by Black's Law Dictionary. This is commonly thought to be unethical and there is an old adage that "eavesdroppers seldom hear anything good of themselves...eavesdroppers always try to listen to matters that concern them."
Traffic analysis - is the process of intercepting and examining messages in order to deduce information from patterns in communication. It can be performed even when the messages are encrypted and cannot be decrypted. In general, the greater the number of messages observed, or even intercepted and stored, the more can be inferred from the traffic. Traffic analysis can be performed in the context of military intelligence, counter-intelligence, or pattern-of-life analysis, and is a concern in computer security.
Masquerading - A masquerade attack is an attack that uses a fake identity, such as a network identity, to gain unauthorized access to personal computer information through legitimate access identification. If an authorization process is not fully protected, it can become extremely vulnerable to a masquerade attack.
Masquerade attacks can be perpetrated using stolen passwords and logons, by locating gaps in programs, or by finding a way around the authentication process. The attack can be triggered either by someone within the organization or by an outsider if the organization is connected to a public network. The amount of access masquerade attackers get depends on the level of authorization they've managed to attain. As such, masquerade attackers can have a full smorgasbord of cyber crime opportunities if they've gained the highest access authority to a business organization. Personal attacks, although less common, can also be harmful.
Following reference(s) were/was used to create this question:
CISA review manual 2014 Page number 322
CISA Exam Question 88
Which of the following is protocol data unit (PDU) of transport layer in TCP/IP model?
Correct Answer: B
Section: Information System Operations, Maintenance and Support
Explanation:
For your exam you should know below information about TCP/IP model:
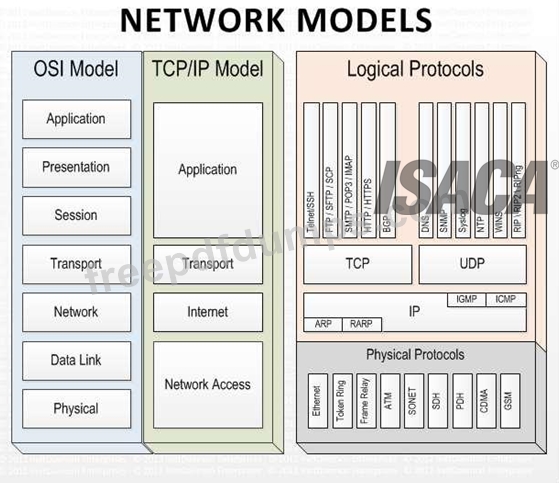
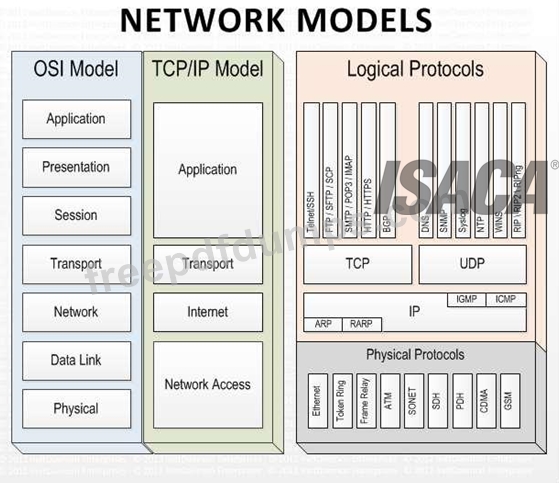
Network models
Layer 4. Application Layer
Application layer is the top most layer of four layer TCP/IP model. Application layer is present on the top of the Transport layer. Application layer defines TCP/IP application protocols and how host programs interface with Transport layer services to use the network.
Application layer includes all the higher-level protocols like DNS (Domain Naming System), HTTP (Hypertext Transfer Protocol), Telnet, SSH, FTP (File Transfer Protocol), TFTP (Trivial File Transfer Protocol), SNMP (Simple Network Management Protocol), SMTP (Simple Mail Transfer Protocol) , DHCP (Dynamic Host Configuration Protocol), X Windows, RDP (Remote Desktop Protocol) etc.
Layer 3. Transport Layer
Transport Layer is the third layer of the four layer TCP/IP model. The position of the Transport layer is between Application layer and Internet layer. The purpose of Transport layer is to permit devices on the source and destination hosts to carry on a conversation. Transport layer defines the level of service and status of the connection used when transporting data.
The main protocols included at Transport layer are TCP (Transmission Control Protocol) and UDP (User Datagram Protocol).
Layer 2. Internet Layer
Internet Layer is the second layer of the four layer TCP/IP model. The position of Internet layer is between Network Access Layer and Transport layer. Internet layer pack data into data packets known as IP datagram's, which contain source and destination address (logical address or IP address) information that is used to forward the datagram's between hosts and across networks. The Internet layer is also responsible for routing of IP datagram's.
Packet switching network depends upon a connectionless internetwork layer. This layer is known as Internet layer. Its job is to allow hosts to insert packets into any network and have them to deliver independently to the destination. At the destination side data packets may appear in a different order than they were sent. It is the job of the higher layers to rearrange them in order to deliver them to proper network applications operating at the Application layer.
The main protocols included at Internet layer are IP (Internet Protocol), ICMP (Internet Control Message Protocol), ARP (Address Resolution Protocol), RARP (Reverse Address Resolution Protocol) and IGMP (Internet Group Management Protocol).
Layer 1. Network Access Layer
Network Access Layer is the first layer of the four layer TCP/IP model. Network Access Layer defines details of how data is physically sent through the network, including how bits are electrically or optically signaled by hardware devices that interface directly with a network medium, such as coaxial cable, optical fiber, or twisted pair copper wire.
The protocols included in Network Access Layer are Ethernet, Token Ring, FDDI, X.25, Frame Relay etc.
The most popular LAN architecture among those listed above is Ethernet. Ethernet uses an Access Method called CSMA/CD (Carrier Sense Multiple Access/Collision Detection) to access the media, when Ethernet operates in a shared media. An Access Method determines how a host will place data on the medium.
IN CSMA/CD Access Method, every host has equal access to the medium and can place data on the wire when the wire is free from network traffic. When a host wants to place data on the wire, it will check the wire to find whether another host is already using the medium. If there is traffic already in the medium, the host will wait and if there is no traffic, it will place the data in the medium. But, if two systems place data on the medium at the same instance, they will collide with each other, destroying the data. If the data is destroyed during transmission, the data will need to be retransmitted. After collision, each host will wait for a small interval of time and again the data will be retransmitted.
Protocol Data Unit (PDU):
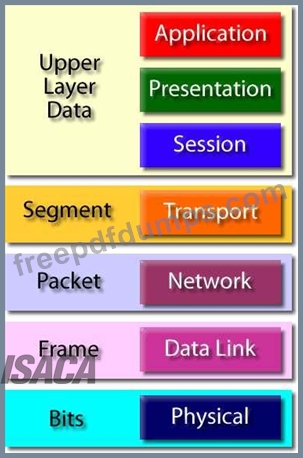
The following answers are incorrect:
Data - Application layer PDU
Packet - Network interface layer PDU
Frame/bit - LAN or WAN interface layer PDU
Reference:
CISA review manual 2014 page number 272
Explanation:
For your exam you should know below information about TCP/IP model:
Network models
Layer 4. Application Layer
Application layer is the top most layer of four layer TCP/IP model. Application layer is present on the top of the Transport layer. Application layer defines TCP/IP application protocols and how host programs interface with Transport layer services to use the network.
Application layer includes all the higher-level protocols like DNS (Domain Naming System), HTTP (Hypertext Transfer Protocol), Telnet, SSH, FTP (File Transfer Protocol), TFTP (Trivial File Transfer Protocol), SNMP (Simple Network Management Protocol), SMTP (Simple Mail Transfer Protocol) , DHCP (Dynamic Host Configuration Protocol), X Windows, RDP (Remote Desktop Protocol) etc.
Layer 3. Transport Layer
Transport Layer is the third layer of the four layer TCP/IP model. The position of the Transport layer is between Application layer and Internet layer. The purpose of Transport layer is to permit devices on the source and destination hosts to carry on a conversation. Transport layer defines the level of service and status of the connection used when transporting data.
The main protocols included at Transport layer are TCP (Transmission Control Protocol) and UDP (User Datagram Protocol).
Layer 2. Internet Layer
Internet Layer is the second layer of the four layer TCP/IP model. The position of Internet layer is between Network Access Layer and Transport layer. Internet layer pack data into data packets known as IP datagram's, which contain source and destination address (logical address or IP address) information that is used to forward the datagram's between hosts and across networks. The Internet layer is also responsible for routing of IP datagram's.
Packet switching network depends upon a connectionless internetwork layer. This layer is known as Internet layer. Its job is to allow hosts to insert packets into any network and have them to deliver independently to the destination. At the destination side data packets may appear in a different order than they were sent. It is the job of the higher layers to rearrange them in order to deliver them to proper network applications operating at the Application layer.
The main protocols included at Internet layer are IP (Internet Protocol), ICMP (Internet Control Message Protocol), ARP (Address Resolution Protocol), RARP (Reverse Address Resolution Protocol) and IGMP (Internet Group Management Protocol).
Layer 1. Network Access Layer
Network Access Layer is the first layer of the four layer TCP/IP model. Network Access Layer defines details of how data is physically sent through the network, including how bits are electrically or optically signaled by hardware devices that interface directly with a network medium, such as coaxial cable, optical fiber, or twisted pair copper wire.
The protocols included in Network Access Layer are Ethernet, Token Ring, FDDI, X.25, Frame Relay etc.
The most popular LAN architecture among those listed above is Ethernet. Ethernet uses an Access Method called CSMA/CD (Carrier Sense Multiple Access/Collision Detection) to access the media, when Ethernet operates in a shared media. An Access Method determines how a host will place data on the medium.
IN CSMA/CD Access Method, every host has equal access to the medium and can place data on the wire when the wire is free from network traffic. When a host wants to place data on the wire, it will check the wire to find whether another host is already using the medium. If there is traffic already in the medium, the host will wait and if there is no traffic, it will place the data in the medium. But, if two systems place data on the medium at the same instance, they will collide with each other, destroying the data. If the data is destroyed during transmission, the data will need to be retransmitted. After collision, each host will wait for a small interval of time and again the data will be retransmitted.
Protocol Data Unit (PDU):
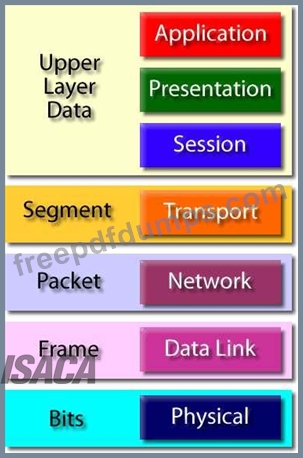
The following answers are incorrect:
Data - Application layer PDU
Packet - Network interface layer PDU
Frame/bit - LAN or WAN interface layer PDU
Reference:
CISA review manual 2014 page number 272
CISA Exam Question 89
An existing system is being replaced with a new application package. User acceptance testing (UAT) should ensure that:
Correct Answer: B
Section: Information System Acquisition, Development and Implementation
CISA Exam Question 90
Which of the following layer of an OSI model responsible for routing and forwarding of a network packets?
Correct Answer: B
Section: Information System Operations, Maintenance and Support
Explanation/Reference:
The network layer controls the operation of the subnet, deciding which physical path the data should take
based on network conditions, priority of service, and other factors.
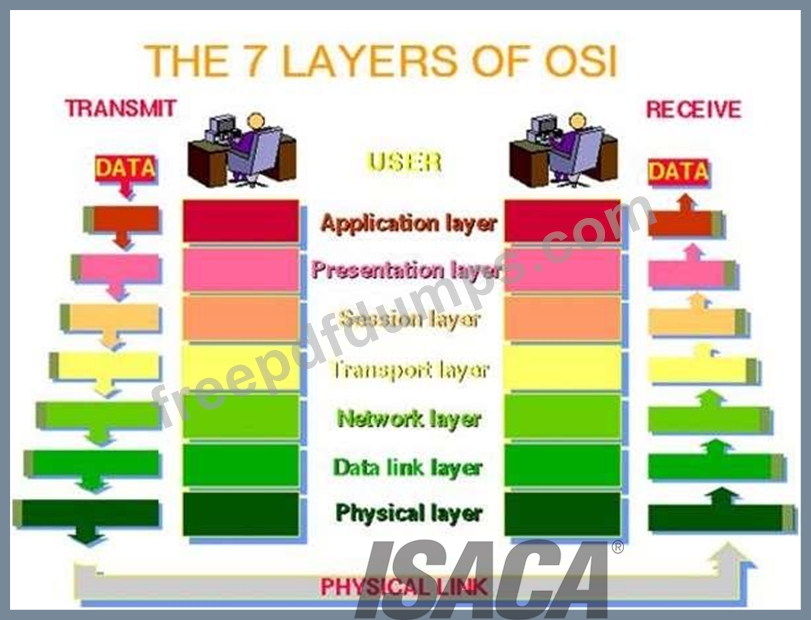
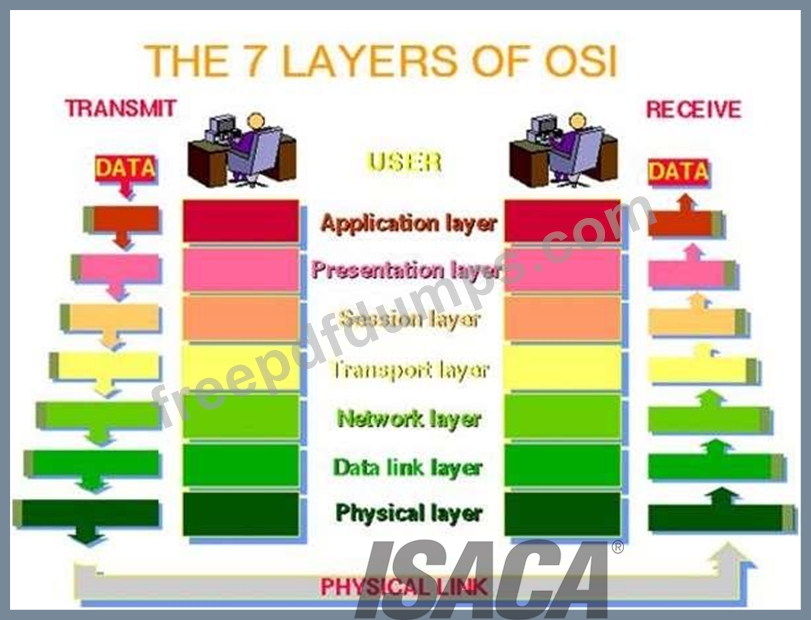
For CISA exam you should know below information about OSI model:
The Open Systems Interconnection model (OSI) is a conceptual model that characterizes and standardizes
the internal functions of a communication system by partitioning it into abstraction layers. The model is a
product of the Open Systems Interconnection project at the International Organization for Standardization
(ISO), maintained by the identification ISO/IEC 7498-1.
The model groups communication functions into seven logical layers. A layer serves the layer above it and
is served by the layer below it. For example, a layer that provides error-free communications across a
network provides the path needed by applications above it, while it calls the next lower layer to send and
receive packets that make up the contents of that path. Two instances at one layer are connected by a
horizontal.OSI Model
PHYSICAL LAYER
The physical layer, the lowest layer of the OSI model, is concerned with the transmission and reception of
the unstructured raw bit stream over a physical medium. It describes the electrical/optical, mechanical, and
functional interfaces to the physical medium, and carries the signals for all of the higher layers. It provides:
Data encoding: modifies the simple digital signal pattern (1s and 0s) used by the PC to better
accommodate the characteristics of the physical medium, and to aid in bit and frame synchronization. It
determines:
What signal state represents a binary 1
How the receiving station knows when a "bit-time" starts
How the receiving station delimits a frame
DATA LINK LAYER
The data link layer provides error-free transfer of data frames from one node to another over the physical
layer, allowing layers above it to assume virtually error-free transmission over the link. To do this, the data
link layer provides:
Link establishment and termination: establishes and terminates the logical link between two nodes.
Frame traffic control: tells the transmitting node to "back-off" when no frame buffers are available.
Frame sequencing: transmits/receives frames sequentially.
Frame acknowledgment: provides/expects frame acknowledgments. Detects and recovers from errors that
occur in the physical layer by retransmitting non-acknowledged frames and handling duplicate frame
receipt.
Frame delimiting: creates and recognizes frame boundaries.
Frame error checking: checks received frames for integrity.
Media access management: determines when the node "has the right" to use the physical medium.
NETWORK LAYER
The network layer controls the operation of the subnet, deciding which physical path the data should take
based on network conditions, priority of service, and other factors. It provides:
Routing: routes frames among networks.
Subnet traffic control: routers (network layer intermediate systems) can instruct a sending station to
"throttle back" its frame transmission when the router's buffer fills up.
Frame fragmentation: if it determines that a downstream router's maximum transmission unit (MTU) size is
less than the frame size, a router can fragment a frame for transmission and re-assembly at the destination
station.
Logical-physical address mapping: translates logical addresses, or names, into physical addresses.
Subnet usage accounting: has accounting functions to keep track of frames forwarded by subnet
intermediate systems, to produce billing information.
Communications Subnet
The network layer software must build headers so that the network layer software residing in the subnet
intermediate systems can recognize them and use them to route data to the destination address.
This layer relieves the upper layers of the need to know anything about the data transmission and
intermediate switching technologies used to connect systems. It establishes, maintains and terminates
connections across the intervening communications facility (one or several intermediate systems in the
communication subnet).
In the network layer and the layers below, peer protocols exist between a node and its immediate neighbor,
but the neighbor may be a node through which data is routed, not the destination station. The source and
destination stations may be separated by many intermediate systems.
TRANSPORT LAYER
The transport layer ensures that messages are delivered error-free, in sequence, and with no losses or
duplications. It relieves the higher layer protocols from any concern with the transfer of data between them
and their peers.
The size and complexity of a transport protocol depends on the type of service it can get from the network
layer. For a reliable network layer with virtual circuit capability, a minimal transport layer is required. If the
network layer is unreliable and/or only supports datagram's, the transport protocol should include extensive
error detection and recovery.
The transport layer provides:
Message segmentation: accepts a message from the (session) layer above it, splits the message into
smaller units (if not already small enough), and passes the smaller units down to the network layer. The
transport layer at the destination station reassembles the message.
Message acknowledgment: provides reliable end-to-end message delivery with acknowledgments.
Message traffic control: tells the transmitting station to "back-off" when no message buffers are available.
Session multiplexing: multiplexes several message streams, or sessions onto one logical link and keeps
track of which messages belong to which sessions (see session layer).
Typically, the transport layer can accept relatively large messages, but there are strict message size limits
imposed by the network (or lower) layer. Consequently, the transport layer must break up the messages
into smaller units, or frames, pretending a header to each frame.
The transport layer header information must then include control information, such as message start and
message end flags, to enable the transport layer on the other end to recognize message boundaries. In
addition, if the lower layers do not maintain sequence, the transport header must contain sequence
information to enable the transport layer on the receiving end to get the pieces back together in the right
order before handing the received message up to the layer above.
End-to-end layers
Unlike the lower "subnet" layers whose protocol is between immediately adjacent nodes, the transport layer
and the layers above are true "source to destination" or end-to-end layers, and are not concerned with the
details of the underlying communications facility. Transport layer software (and software above it) on the
source station carries on a conversation with similar software on the destination station by using message
headers and control messages.
SESSION LAYER
The session layer allows session establishment between processes running on different stations. It
provides:
Session establishment, maintenance and termination: allows two application processes on different
machines to establish, use and terminate a connection, called a session.
Session support: performs the functions that allow these processes to communicate over the network,
performing security, name recognition, logging, and so on.
PRESENTATION LAYER
The presentation layer formats the data to be presented to the application layer. It can be viewed as the
translator for the network. This layer may translate data from a format used by the application layer into a
common format at the sending station, then translate the common format to a format known to the
application layer at the receiving station.
The presentation layer provides:
Character code translation: for example, ASCII to EBCDIC.
Data conversion: bit order, CR-CR/LF, integer-floating point, and so on.
Data compression: reduces the number of bits that need to be transmitted on the network.
Data encryption: encrypt data for security purposes. For example, password encryption.
APPLICATION LAYER
The application layer serves as the window for users and application processes to access network
services. This layer contains a variety of commonly needed functions:
Resource sharing and device redirection
Remote file access
Remote printer access
Inter-process communication
Network management
Directory services
Electronic messaging (such as mail)
Network virtual terminals
The following were incorrect answers:
Transport layer - The transport layer ensures that messages are delivered error-free, in sequence, and with
no losses or duplications. It relieves the higher layer protocols from any concern with the transfer of data
between them and their peers.
Data link layer - The data link layer provides error-free transfer of data frames from one node to another
over the physical layer, allowing layers above it to assume virtually error-free transmission over the link.
Physical Layer - The physical layer, the lowest layer of the OSI model, is concerned with the transmission
and reception of the unstructured raw bit stream over a physical medium. It describes the electrical/optical,
mechanical, and functional interfaces to the physical medium, and carries the signals for all of the higher
layers.
The following reference(s) were/was used to create this question:
CISA review manual 2014 Page number 260
Explanation/Reference:
The network layer controls the operation of the subnet, deciding which physical path the data should take
based on network conditions, priority of service, and other factors.
For CISA exam you should know below information about OSI model:
The Open Systems Interconnection model (OSI) is a conceptual model that characterizes and standardizes
the internal functions of a communication system by partitioning it into abstraction layers. The model is a
product of the Open Systems Interconnection project at the International Organization for Standardization
(ISO), maintained by the identification ISO/IEC 7498-1.
The model groups communication functions into seven logical layers. A layer serves the layer above it and
is served by the layer below it. For example, a layer that provides error-free communications across a
network provides the path needed by applications above it, while it calls the next lower layer to send and
receive packets that make up the contents of that path. Two instances at one layer are connected by a
horizontal.OSI Model
PHYSICAL LAYER
The physical layer, the lowest layer of the OSI model, is concerned with the transmission and reception of
the unstructured raw bit stream over a physical medium. It describes the electrical/optical, mechanical, and
functional interfaces to the physical medium, and carries the signals for all of the higher layers. It provides:
Data encoding: modifies the simple digital signal pattern (1s and 0s) used by the PC to better
accommodate the characteristics of the physical medium, and to aid in bit and frame synchronization. It
determines:
What signal state represents a binary 1
How the receiving station knows when a "bit-time" starts
How the receiving station delimits a frame
DATA LINK LAYER
The data link layer provides error-free transfer of data frames from one node to another over the physical
layer, allowing layers above it to assume virtually error-free transmission over the link. To do this, the data
link layer provides:
Link establishment and termination: establishes and terminates the logical link between two nodes.
Frame traffic control: tells the transmitting node to "back-off" when no frame buffers are available.
Frame sequencing: transmits/receives frames sequentially.
Frame acknowledgment: provides/expects frame acknowledgments. Detects and recovers from errors that
occur in the physical layer by retransmitting non-acknowledged frames and handling duplicate frame
receipt.
Frame delimiting: creates and recognizes frame boundaries.
Frame error checking: checks received frames for integrity.
Media access management: determines when the node "has the right" to use the physical medium.
NETWORK LAYER
The network layer controls the operation of the subnet, deciding which physical path the data should take
based on network conditions, priority of service, and other factors. It provides:
Routing: routes frames among networks.
Subnet traffic control: routers (network layer intermediate systems) can instruct a sending station to
"throttle back" its frame transmission when the router's buffer fills up.
Frame fragmentation: if it determines that a downstream router's maximum transmission unit (MTU) size is
less than the frame size, a router can fragment a frame for transmission and re-assembly at the destination
station.
Logical-physical address mapping: translates logical addresses, or names, into physical addresses.
Subnet usage accounting: has accounting functions to keep track of frames forwarded by subnet
intermediate systems, to produce billing information.
Communications Subnet
The network layer software must build headers so that the network layer software residing in the subnet
intermediate systems can recognize them and use them to route data to the destination address.
This layer relieves the upper layers of the need to know anything about the data transmission and
intermediate switching technologies used to connect systems. It establishes, maintains and terminates
connections across the intervening communications facility (one or several intermediate systems in the
communication subnet).
In the network layer and the layers below, peer protocols exist between a node and its immediate neighbor,
but the neighbor may be a node through which data is routed, not the destination station. The source and
destination stations may be separated by many intermediate systems.
TRANSPORT LAYER
The transport layer ensures that messages are delivered error-free, in sequence, and with no losses or
duplications. It relieves the higher layer protocols from any concern with the transfer of data between them
and their peers.
The size and complexity of a transport protocol depends on the type of service it can get from the network
layer. For a reliable network layer with virtual circuit capability, a minimal transport layer is required. If the
network layer is unreliable and/or only supports datagram's, the transport protocol should include extensive
error detection and recovery.
The transport layer provides:
Message segmentation: accepts a message from the (session) layer above it, splits the message into
smaller units (if not already small enough), and passes the smaller units down to the network layer. The
transport layer at the destination station reassembles the message.
Message acknowledgment: provides reliable end-to-end message delivery with acknowledgments.
Message traffic control: tells the transmitting station to "back-off" when no message buffers are available.
Session multiplexing: multiplexes several message streams, or sessions onto one logical link and keeps
track of which messages belong to which sessions (see session layer).
Typically, the transport layer can accept relatively large messages, but there are strict message size limits
imposed by the network (or lower) layer. Consequently, the transport layer must break up the messages
into smaller units, or frames, pretending a header to each frame.
The transport layer header information must then include control information, such as message start and
message end flags, to enable the transport layer on the other end to recognize message boundaries. In
addition, if the lower layers do not maintain sequence, the transport header must contain sequence
information to enable the transport layer on the receiving end to get the pieces back together in the right
order before handing the received message up to the layer above.
End-to-end layers
Unlike the lower "subnet" layers whose protocol is between immediately adjacent nodes, the transport layer
and the layers above are true "source to destination" or end-to-end layers, and are not concerned with the
details of the underlying communications facility. Transport layer software (and software above it) on the
source station carries on a conversation with similar software on the destination station by using message
headers and control messages.
SESSION LAYER
The session layer allows session establishment between processes running on different stations. It
provides:
Session establishment, maintenance and termination: allows two application processes on different
machines to establish, use and terminate a connection, called a session.
Session support: performs the functions that allow these processes to communicate over the network,
performing security, name recognition, logging, and so on.
PRESENTATION LAYER
The presentation layer formats the data to be presented to the application layer. It can be viewed as the
translator for the network. This layer may translate data from a format used by the application layer into a
common format at the sending station, then translate the common format to a format known to the
application layer at the receiving station.
The presentation layer provides:
Character code translation: for example, ASCII to EBCDIC.
Data conversion: bit order, CR-CR/LF, integer-floating point, and so on.
Data compression: reduces the number of bits that need to be transmitted on the network.
Data encryption: encrypt data for security purposes. For example, password encryption.
APPLICATION LAYER
The application layer serves as the window for users and application processes to access network
services. This layer contains a variety of commonly needed functions:
Resource sharing and device redirection
Remote file access
Remote printer access
Inter-process communication
Network management
Directory services
Electronic messaging (such as mail)
Network virtual terminals
The following were incorrect answers:
Transport layer - The transport layer ensures that messages are delivered error-free, in sequence, and with
no losses or duplications. It relieves the higher layer protocols from any concern with the transfer of data
between them and their peers.
Data link layer - The data link layer provides error-free transfer of data frames from one node to another
over the physical layer, allowing layers above it to assume virtually error-free transmission over the link.
Physical Layer - The physical layer, the lowest layer of the OSI model, is concerned with the transmission
and reception of the unstructured raw bit stream over a physical medium. It describes the electrical/optical,
mechanical, and functional interfaces to the physical medium, and carries the signals for all of the higher
layers.
The following reference(s) were/was used to create this question:
CISA review manual 2014 Page number 260
- Other Version
- 735ISACA.CISA.v2025-12-09.q630
- 415ISACA.CISA.v2025-12-02.q704
- 10549ISACA.CISA.v2025-06-20.q647
- 3541ISACA.CISA.v2025-06-11.q606
- 3416ISACA.CISA.v2023-03-04.q272
- 2658ISACA.CISA.v2022-10-31.q203
- 123ISACA.Examprepaway.CISA.v2022-02-10.by.barret.126q.pdf
- 9021ISACA.CISA.v2021-11-29.q567
- 36ISACA.Actualvce.CISA.v2021-08-31.by.ralap.101q.pdf
- Latest Upload
- 119SAP.C_BCBAI_2509.v2026-01-15.q13
- 198DAMA.DMF-1220.v2026-01-15.q271
- 138SAP.C_SIGDA_2403.v2026-01-15.q66
- 188ISACA.CRISC.v2026-01-15.q649
- 128PaloAltoNetworks.NetSec-Pro.v2026-01-15.q26
- 170Splunk.SPLK-1002.v2026-01-14.q121
- 170EMC.NCP-AII.v2026-01-14.q144
- 164Microsoft.AZ-800.v2026-01-13.q144
- 176Microsoft.MS-102.v2026-01-13.q258
- 121HP.HPE2-E84.v2026-01-13.q17
[×]
Download PDF File
Enter your email address to download ISACA.CISA.v2022-03-29.q126 Practice Test

