CISA Exam Question 121
Which of the following attack best describe "Computer is the target of a crime" and "Computer is the tool of a crime"?
Correct Answer: A
Explanation/Reference:
In computing, a denial-of-service (DoS) or distributed denial-of-service (DDoS) attack is an attempt to make a machine or network resource unavailable to its intended users. Although the means to carry out, motives for, and targets of a DoS attack may vary, it generally consists of efforts to temporarily or indefinitely interrupt or suspend services of a host connected to the Internet. As clarification, DDoS (Distributed Denial of Service) attacks are sent by two or more persons, or bots. (See botnet) DoS (Denial of Service) attacks are sent by one person or system.
Keystroke logging, often referred to as key logging or keyboard capturing, is the action of recording (or logging) the keys struck on a keyboard, typically in a covert manner so that the person using the keyboard is unaware that their actions are being monitored. It also has very legitimate uses in studies of human- computer interaction. There are numerous key logging methods, ranging from hardware and software- based approaches to acoustic analysis.
There are four types of a computer crimes:
1. Computer is the target of a crime - Perpetrator uses another computer to launch an attack. In this attack the target is a specific identified computer. Ex. Denial of Service (DoS), hacking
2. Computer is the Subject of a crime - In this attack perpetrator uses computer to commit crime and the target is another computer. In this attack, target may or may not be defined. Perpetrator launches attack with no specific target in mind. Ex. Distributed DoS, Malware
3. Computer is the tool of a crime - Perpetrator uses computer to commit crime but the target is not a computer. Target is the data or information stored on a computer. Ex. Fraud, unauthorized access, phishing, installing key logger
4. Computer Symbolizes Crime - Perpetrator lures the user of a computer to get confidential information.
Target is user of computer. Ex. Social engineering methods like Phishing, Fake website, Scam Mails, etc The following answers are incorrect:
Eavesdropping - is the act of secretly listening to the private conversation of others without their consent, as defined by Black's Law Dictionary. This is commonly thought to be unethical and there is an old adage that "eavesdroppers seldom hear anything good of themselves...eavesdroppers always try to listen to matters that concern them." Traffic analysis - is the process of intercepting and examining messages in order to deduce information from patterns in communication. It can be performed even when the messages are encrypted and cannot be decrypted. In general, the greater the number of messages observed, or even intercepted and stored, the more can be inferred from the traffic. Traffic analysis can be performed in the context of military intelligence, counter-intelligence, or pattern-of-life analysis, and is a concern in computer security.
Masquerading - A masquerade attack is an attack that uses a fake identity, such as a network identity, to gain unauthorized access to personal computer information through legitimate access identification. If an authorization process is not fully protected, it can become extremely vulnerable to a masquerade attack.
Masquerade attacks can be perpetrated using stolen passwords and logons, by locating gaps in programs, or by finding a way around the authentication process. The attack can be triggered either by someone within the organization or by an outsider if the organization is connected to a public network. The amount of access masquerade attackers get depends on the level of authorization they've managed to attain. As such, masquerade attackers can have a full smorgasbord of cybercrime opportunities if they've gained the highest access authority to a business organization. Personal attacks, although less common, can also be harmful.
The following reference(s) were/was used to create this question:
CISA review Manual 2014. Page number 321
http://en.wikipedia.org/wiki/Denial-of-service_attack
http://en.wikipedia.org/wiki/Eavesdropping
http://en.wikipedia.org/wiki/Traffic_analysis
http://www.techopedia.com/definition/4020/masquerade-attack
In computing, a denial-of-service (DoS) or distributed denial-of-service (DDoS) attack is an attempt to make a machine or network resource unavailable to its intended users. Although the means to carry out, motives for, and targets of a DoS attack may vary, it generally consists of efforts to temporarily or indefinitely interrupt or suspend services of a host connected to the Internet. As clarification, DDoS (Distributed Denial of Service) attacks are sent by two or more persons, or bots. (See botnet) DoS (Denial of Service) attacks are sent by one person or system.
Keystroke logging, often referred to as key logging or keyboard capturing, is the action of recording (or logging) the keys struck on a keyboard, typically in a covert manner so that the person using the keyboard is unaware that their actions are being monitored. It also has very legitimate uses in studies of human- computer interaction. There are numerous key logging methods, ranging from hardware and software- based approaches to acoustic analysis.
There are four types of a computer crimes:
1. Computer is the target of a crime - Perpetrator uses another computer to launch an attack. In this attack the target is a specific identified computer. Ex. Denial of Service (DoS), hacking
2. Computer is the Subject of a crime - In this attack perpetrator uses computer to commit crime and the target is another computer. In this attack, target may or may not be defined. Perpetrator launches attack with no specific target in mind. Ex. Distributed DoS, Malware
3. Computer is the tool of a crime - Perpetrator uses computer to commit crime but the target is not a computer. Target is the data or information stored on a computer. Ex. Fraud, unauthorized access, phishing, installing key logger
4. Computer Symbolizes Crime - Perpetrator lures the user of a computer to get confidential information.
Target is user of computer. Ex. Social engineering methods like Phishing, Fake website, Scam Mails, etc The following answers are incorrect:
Eavesdropping - is the act of secretly listening to the private conversation of others without their consent, as defined by Black's Law Dictionary. This is commonly thought to be unethical and there is an old adage that "eavesdroppers seldom hear anything good of themselves...eavesdroppers always try to listen to matters that concern them." Traffic analysis - is the process of intercepting and examining messages in order to deduce information from patterns in communication. It can be performed even when the messages are encrypted and cannot be decrypted. In general, the greater the number of messages observed, or even intercepted and stored, the more can be inferred from the traffic. Traffic analysis can be performed in the context of military intelligence, counter-intelligence, or pattern-of-life analysis, and is a concern in computer security.
Masquerading - A masquerade attack is an attack that uses a fake identity, such as a network identity, to gain unauthorized access to personal computer information through legitimate access identification. If an authorization process is not fully protected, it can become extremely vulnerable to a masquerade attack.
Masquerade attacks can be perpetrated using stolen passwords and logons, by locating gaps in programs, or by finding a way around the authentication process. The attack can be triggered either by someone within the organization or by an outsider if the organization is connected to a public network. The amount of access masquerade attackers get depends on the level of authorization they've managed to attain. As such, masquerade attackers can have a full smorgasbord of cybercrime opportunities if they've gained the highest access authority to a business organization. Personal attacks, although less common, can also be harmful.
The following reference(s) were/was used to create this question:
CISA review Manual 2014. Page number 321
http://en.wikipedia.org/wiki/Denial-of-service_attack
http://en.wikipedia.org/wiki/Eavesdropping
http://en.wikipedia.org/wiki/Traffic_analysis
http://www.techopedia.com/definition/4020/masquerade-attack
CISA Exam Question 122
Which of the following type of a computer network is a WAN that are limited to a city?
Correct Answer: B
Explanation/Reference:
MAN - A metropolitan area network (MAN) is a computer network in which two or more computers or communicating devices or networks which are geographically separated but in same metropolitan city and are connected to each other are said to be connected on MAN. Metropolitan limits are determined by local municipal corporations; the larger the city, the bigger the MAN, the smaller a metro city, smaller the MAN.
For your exam you should know below information about computer networks:
Local Area Network (LAN)
A local area network (LAN) is a computer network that interconnects computers within a limited area such as a home, school, computer laboratory, or office building using network media.
Local Area Network

Wide Area Network
A wide area network (WAN) is a network that covers a broad area (i.e., any telecommunications network that links across metropolitan, regional, national or international boundaries) using leased telecommunication lines.
Wide Area Network
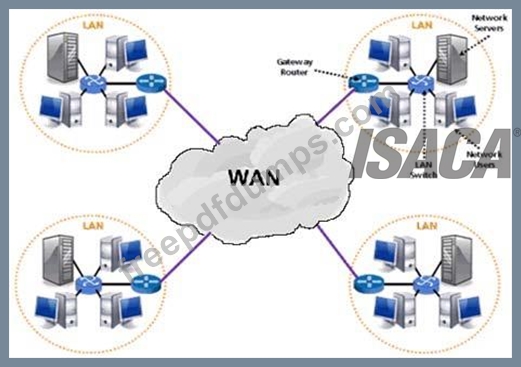
Source of image: http://www.netprivateer.com/images/lanwan.gif
Metropolitan Area Network
A metropolitan area network (MAN) is a computer network in which two or more computers or communicating devices or networks which are geographically separated but in same metropolitan city and are connected to each other are said to be connected on MAN. Metropolitan limits are determined by local municipal corporations; the larger the city, the bigger the MAN, the smaller a metro city, smaller the MAN Metropolitan Area Network
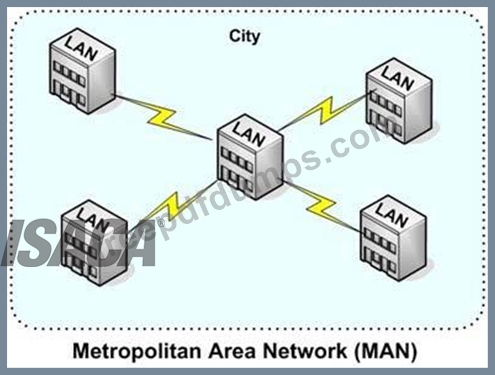
Source of image: http://cis.msjc.edu/courses/images/MAN.jpg
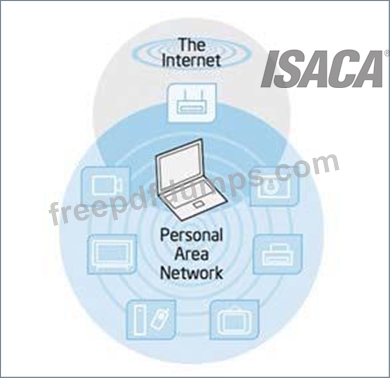
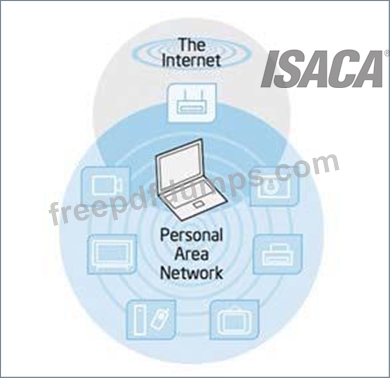
Personal Area Network
A personal area network (PAN) is a computer network used for data transmission among devices such as computers, telephones and personal digital assistants. PANs can be used for communication among the personal devices themselves (intrapersonal communication), or for connecting to a higher level network and the Internet (an uplink).
Personal Area Network
Click HERE for original image
Storage Area Network
A storage area network (SAN) is a dedicated network that provides access to consolidated, block level data storage. SANs are primarily used to enhance storage devices, such as disk arrays, tape libraries, and optical jukeboxes, accessible to servers so that the devices appear like locally attached devices to the operating system. A SAN typically has its own network of storage devices that are generally not accessible through the local area network (LAN) by other devices.
Storage Area Network
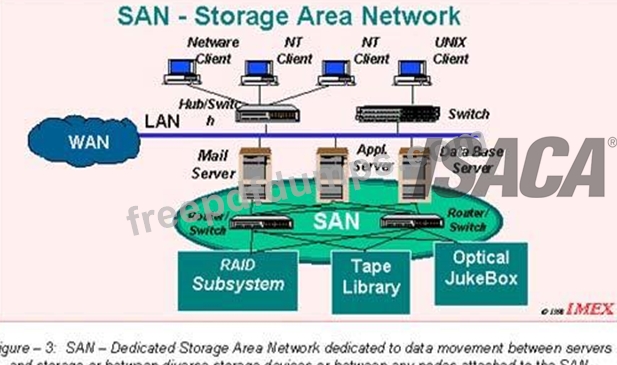
Source of image: http://www.imexresearch.com/images/sasnassan-3.gif
The following were incorrect answers:
PAN - A personal area network (PAN) is a computer network used for data transmission among devices such as computers, telephones and personal digital assistants. PANs can be used for communication among the personal devices themselves (intrapersonal communication), or for connecting to a higher level network and the Internet (an uplink).
LAN - A local area network (LAN) is a computer network that interconnects computers within a limited area such as a home, school, computer laboratory, or office building using network media.
SAN - A storage area network (SAN) is a dedicated network that provides access to consolidated, block level data storage. SANs are primarily used to enhance storage devices, such as disk arrays, tape libraries, and optical jukeboxes, accessible to servers so that the devices appear like locally attached devices to the operating system. A SAN typically has its own network of storage devices that are generally not accessible through the local area network (LAN) by other devices.
The following reference(s) were/was used to create this question:
CISA review manual 2014 Page number 258
MAN - A metropolitan area network (MAN) is a computer network in which two or more computers or communicating devices or networks which are geographically separated but in same metropolitan city and are connected to each other are said to be connected on MAN. Metropolitan limits are determined by local municipal corporations; the larger the city, the bigger the MAN, the smaller a metro city, smaller the MAN.
For your exam you should know below information about computer networks:
Local Area Network (LAN)
A local area network (LAN) is a computer network that interconnects computers within a limited area such as a home, school, computer laboratory, or office building using network media.
Local Area Network

Wide Area Network
A wide area network (WAN) is a network that covers a broad area (i.e., any telecommunications network that links across metropolitan, regional, national or international boundaries) using leased telecommunication lines.
Wide Area Network
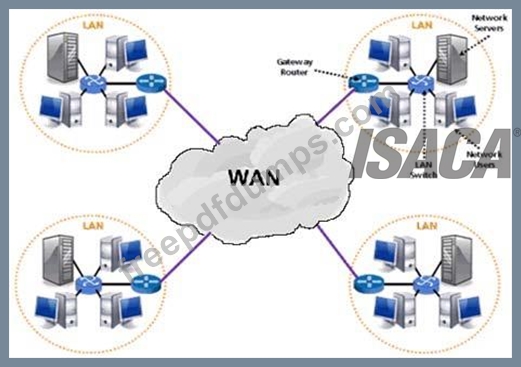
Source of image: http://www.netprivateer.com/images/lanwan.gif
Metropolitan Area Network
A metropolitan area network (MAN) is a computer network in which two or more computers or communicating devices or networks which are geographically separated but in same metropolitan city and are connected to each other are said to be connected on MAN. Metropolitan limits are determined by local municipal corporations; the larger the city, the bigger the MAN, the smaller a metro city, smaller the MAN Metropolitan Area Network
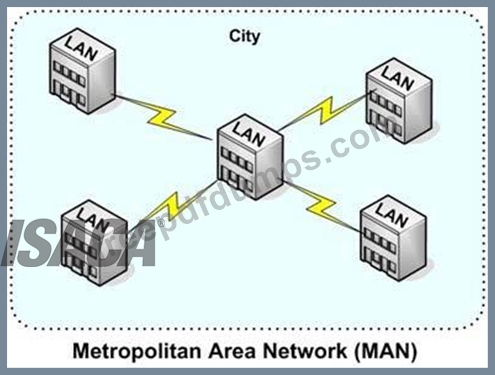
Source of image: http://cis.msjc.edu/courses/images/MAN.jpg
Personal Area Network
A personal area network (PAN) is a computer network used for data transmission among devices such as computers, telephones and personal digital assistants. PANs can be used for communication among the personal devices themselves (intrapersonal communication), or for connecting to a higher level network and the Internet (an uplink).
Personal Area Network
Click HERE for original image
Storage Area Network
A storage area network (SAN) is a dedicated network that provides access to consolidated, block level data storage. SANs are primarily used to enhance storage devices, such as disk arrays, tape libraries, and optical jukeboxes, accessible to servers so that the devices appear like locally attached devices to the operating system. A SAN typically has its own network of storage devices that are generally not accessible through the local area network (LAN) by other devices.
Storage Area Network
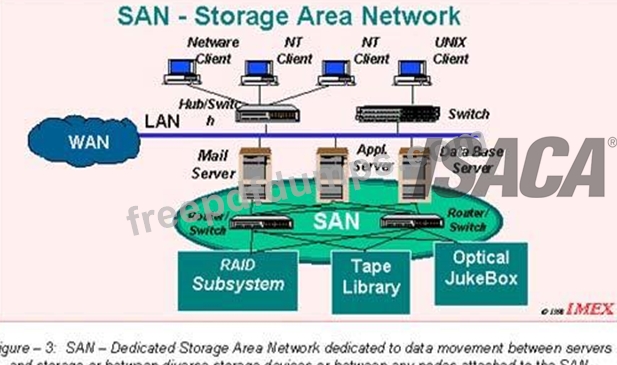
Source of image: http://www.imexresearch.com/images/sasnassan-3.gif
The following were incorrect answers:
PAN - A personal area network (PAN) is a computer network used for data transmission among devices such as computers, telephones and personal digital assistants. PANs can be used for communication among the personal devices themselves (intrapersonal communication), or for connecting to a higher level network and the Internet (an uplink).
LAN - A local area network (LAN) is a computer network that interconnects computers within a limited area such as a home, school, computer laboratory, or office building using network media.
SAN - A storage area network (SAN) is a dedicated network that provides access to consolidated, block level data storage. SANs are primarily used to enhance storage devices, such as disk arrays, tape libraries, and optical jukeboxes, accessible to servers so that the devices appear like locally attached devices to the operating system. A SAN typically has its own network of storage devices that are generally not accessible through the local area network (LAN) by other devices.
The following reference(s) were/was used to create this question:
CISA review manual 2014 Page number 258
CISA Exam Question 123
Which of the following should be of PRIMARY concern to an IS auditor reviewing the management of external IT service providers?
Correct Answer: D
Section: Protection of Information Assets
Explanation:
From an IS auditor's perspective, the primary objective of auditing the management of service providers should be to determine if the services that were requested were provided in a way that is acceptable, seamless and in line with contractual agreements. Minimizing costs, if applicable and achievable (depending on the customer's need) is traditionally not part of an IS auditor's job. This would normally be done by a line management function within the IT department.
Furthermore, during an audit, it is too late to minimize the costs for existing provider arrangements.
Subcontracting providers could be a concern, but it would not be the primary concern. Transferring knowledge to the internal IT department might be desirable under certain circumstances, but should not be the primary concern of an IS auditor when auditing IT service providers and the management thereof.
Explanation:
From an IS auditor's perspective, the primary objective of auditing the management of service providers should be to determine if the services that were requested were provided in a way that is acceptable, seamless and in line with contractual agreements. Minimizing costs, if applicable and achievable (depending on the customer's need) is traditionally not part of an IS auditor's job. This would normally be done by a line management function within the IT department.
Furthermore, during an audit, it is too late to minimize the costs for existing provider arrangements.
Subcontracting providers could be a concern, but it would not be the primary concern. Transferring knowledge to the internal IT department might be desirable under certain circumstances, but should not be the primary concern of an IS auditor when auditing IT service providers and the management thereof.
CISA Exam Question 124
What is a primary high-level goal for an auditor who is reviewing a system development project?
Correct Answer: C
Explanation/Reference:
A primary high-level goal for an auditor who is reviewing a systems-development project is to ensure that business objectives are achieved. This objective guides all other systems development objectives.
A primary high-level goal for an auditor who is reviewing a systems-development project is to ensure that business objectives are achieved. This objective guides all other systems development objectives.
CISA Exam Question 125
A trojan horse simply cannot operate autonomously.
Correct Answer: A
As a common type of Trojan horses, a legitimate software might have been corrupted with malicious code which runs when the program is used. The key is that the user has to invoke the program in order to trigger the malicious code. In other words, a trojan horse simply cannot operate autonomously. You would also want to know that most but not all trojan horse payloads are harmful - a few of them are harmless.
- Other Version
- 737ISACA.CISA.v2025-12-09.q630
- 415ISACA.CISA.v2025-12-02.q704
- 10572ISACA.CISA.v2025-06-20.q647
- 3560ISACA.CISA.v2025-06-11.q606
- 3437ISACA.CISA.v2023-03-04.q272
- 2613ISACA.CISA.v2022-03-29.q126
- 123ISACA.Examprepaway.CISA.v2022-02-10.by.barret.126q.pdf
- 9039ISACA.CISA.v2021-11-29.q567
- 36ISACA.Actualvce.CISA.v2021-08-31.by.ralap.101q.pdf
- Latest Upload
- 119SAP.C_BCBAI_2509.v2026-01-15.q13
- 214DAMA.DMF-1220.v2026-01-15.q271
- 138SAP.C_SIGDA_2403.v2026-01-15.q66
- 218ISACA.CRISC.v2026-01-15.q649
- 128PaloAltoNetworks.NetSec-Pro.v2026-01-15.q26
- 170Splunk.SPLK-1002.v2026-01-14.q121
- 170EMC.NCP-AII.v2026-01-14.q144
- 164Microsoft.AZ-800.v2026-01-13.q144
- 176Microsoft.MS-102.v2026-01-13.q258
- 122HP.HPE2-E84.v2026-01-13.q17
[×]
Download PDF File
Enter your email address to download ISACA.CISA.v2022-10-31.q203 Practice Test

