SY0-601 Exam Question 16
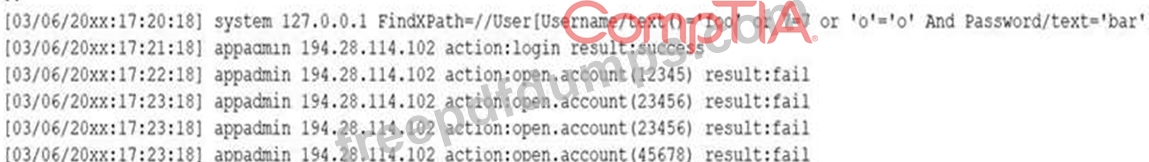
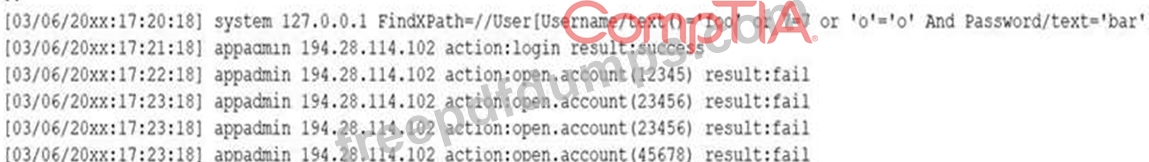
A security analyst receives a SIEM alert that someone logged in to the appadmin test account, which is only used for the early detection of attacks. The security analyst then reviews the following application log:
Which of the following can the security analyst conclude?
Which of the following can the security analyst conclude?
SY0-601 Exam Question 17
A company's Chief Information Officer (CIO) is meeting with the Chief Information Security Officer (CISO) to plan some activities to enhance the skill levels of the company's developers. Which of the following would be MOST suitable for training the developers?
SY0-601 Exam Question 18
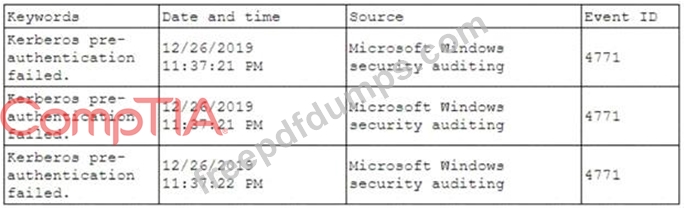
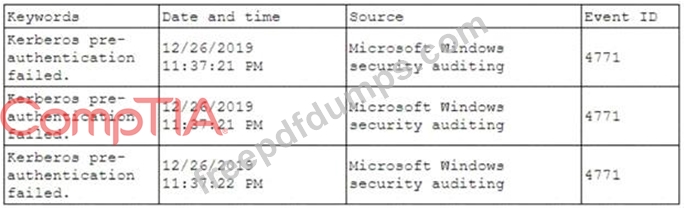
A security analyst has been asked to investigate a situation after the SOC started to receive alerts from the SIEM. The analyst first looks at the domain controller and finds the following events:
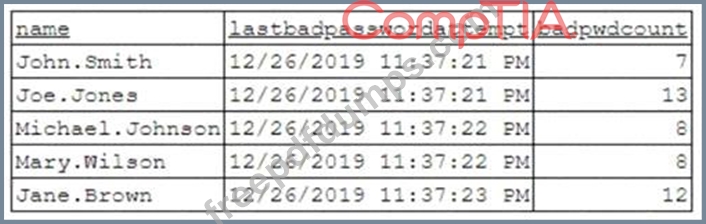
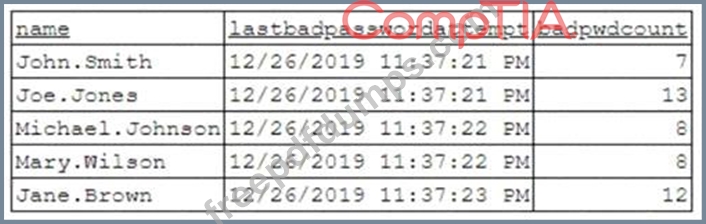
To better understand what is going on, the analyst runs a command and receives the following output:
Based on the analyst's findings, which of the following attacks is being executed?
To better understand what is going on, the analyst runs a command and receives the following output:
Based on the analyst's findings, which of the following attacks is being executed?
SY0-601 Exam Question 19
A security analyst is configuring a large number of new company-issued laptops. The analyst received the following requirements:
* The devices will be used internationally by staff who travel extensively.
* Occasional personal use is acceptable due to the travel requirements.
* Users must be able to install and configure sanctioned programs and productivity suites.
* The devices must be encrypted
* The devices must be capable of operating in low-bandwidth environments.
Which of the following would provide the GREATEST benefit to the security posture of the devices?
* The devices will be used internationally by staff who travel extensively.
* Occasional personal use is acceptable due to the travel requirements.
* Users must be able to install and configure sanctioned programs and productivity suites.
* The devices must be encrypted
* The devices must be capable of operating in low-bandwidth environments.
Which of the following would provide the GREATEST benefit to the security posture of the devices?
SY0-601 Exam Question 20
A security audit has revealed that a process control terminal is vulnerable to malicious users installing and executing software on the system. The terminal is beyond end-of-life support and cannot be upgraded, so it is placed on a projected network segment. Which of the following would be MOST effective to implement to further mitigate the reported vulnerability?

