SY0-601 Exam Question 361
An organization suffered an outage and a critical system took 90 minutes to come back online. Though there was no data loss during the outage, the expectation was that the critical system would be available again within 60 minutes Which of the following is the 60-minute expectation an example of:
SY0-601 Exam Question 362
When implementing automation with loT devices, which of the following should be considered FIRST to keep the network secure?
SY0-601 Exam Question 363
An analyst visits an internet forum looking for information about a tool. The analyst finds a threat that appears to contain relevant information. One of the posts says the following:
Which of the following BEST describes the attack that was attempted against the forum readers?
Which of the following BEST describes the attack that was attempted against the forum readers?
SY0-601 Exam Question 364
A security analyst needs to determine how an attacker was able to use User3 to gain a foothold within a company's network. The company's lockout policy requires that an account be locked out for a minimum of 15 minutes after three unsuccessful attempts. While reviewing the log files, the analyst discovers the following:
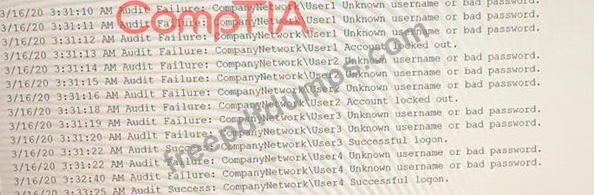
Which of the following attacks MOST likely occurred?
Which of the following attacks MOST likely occurred?
SY0-601 Exam Question 365
A security analyst is reviewing a penetration-testing report from a third-party contractor. The penetration testers used the organization's new API to bypass a driver to perform privilege escalation on the organization's web servers. Upon looking at the API, the security analyst realizes the particular API call was to a legacy system running an outdated OS. Which of the following is the MOST likely attack type?

